Advanced Threat Hunting With Endpoint Detection And Response
Advanced threat hunting is a proactive approach to cybersecurity that involves actively searching for malicious activities and attacks in an organization’s network. It goes beyond traditional security measures such as firewalls and antivirus software, which often focus on prevention rather than detection.
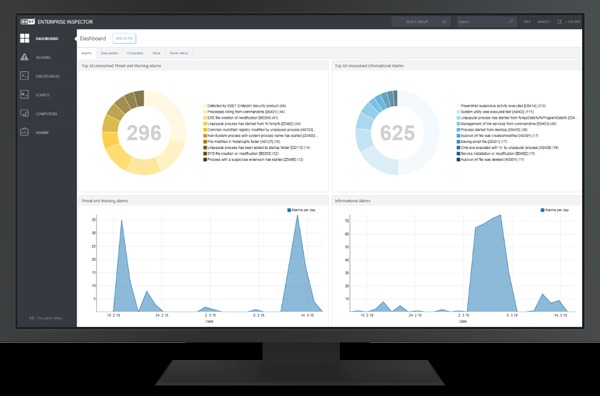
Endpoint Detection and Response (EDR) is a type of security technology that provides visibility into endpoint activity, detects threats in real-time, and responds to them immediately. With endpoint detection and response, defenders can spot what automated tools miss.
What is threat hunting?
Threat hunting is proactive security work. Instead of waiting for alerts, hunters look for signs of intrusion. They ask questions like “Why is this system slow?” or “Who accessed this file at 3 a.m.?” This approach finds attackers who hide in plain sight.
Why endpoints matter:
Endpoints are devices like laptops, servers, and workstations. They hold data and connect to networks. Attackers often target them first. Watching endpoint activity gives clues about malicious behavior. Memory changes, odd process starts, and unusual logins are all red flags.
Start with a strong hypothesis:
Good hunts begin with a guess. Maybe attackers are using a new file type. Maybe old credentials are being tested. A clear idea gives direction. Hunters test their theory by checking logs, processes, and system changes. This keeps the search focused and efficient.
Look for the unknown:
Automated tools detect known threats. Threat hunting finds the unknown. This includes zero day exploits, fileless attacks, and insider misuse. Hunters look for patterns that deviate from normal behavior. A single odd registry change may be the first sign of a larger breach.
Use data to tell a story:
Security tools collect massive amounts of data. Threat hunters sift through this information to build a timeline. They connect small events across multiple devices. A phishing email, a downloaded file, and a strange network connection might form a complete attack chain.
Collaborate and share findings:
Hunting is not a solo task. Teams benefit from sharing what they learn. A finding in one department may apply to another. Documenting the process helps improve future hunts. It also strengthens the overall security posture.
Threat hunting turns defense into an active practice. It moves beyond waiting for alerts. With endpoint detection and response, teams gain visibility into the smallest system changes. Every hunt adds to the collective knowledge of the organization. Staying ahead of attackers requires curiosity, skill, and the right tools.

